記事
-

How Modern Supply Chain Planning Solutions Are Transforming Business Operations
In today’s fast-moving global economy, organizations must manage complex supply chains that span multiple suppliers, distribution networks, and customer channels. Uncertain demand, geopolitical risks...
-

Security Orchestration, Automation, and Response (SOAR): A Key Technology for Modern Cyber Defense
As cyber threats grow more sophisticated and frequent, organizations are under increasing pressure to respond to security incidents faster and more efficiently. Security teams often manage thousands ...
-

Transform Your Cybersecurity Strategy with Continuous Exposure Validation
In the fast-evolving world of cybersecurity, exposure management has become an essential strategy for organisations seeking to reduce risk and strengthen resilience against modern cyber threats. Acco...
-

Strengthening Network Security with Next-Gen NDR Solutions in 2026
In the rapidly changing world of cybersecurity, Network Detection and Response (NDR) solutions have become essential tools for protecting digital networks from advanced threats. NDR technologies cont...
-
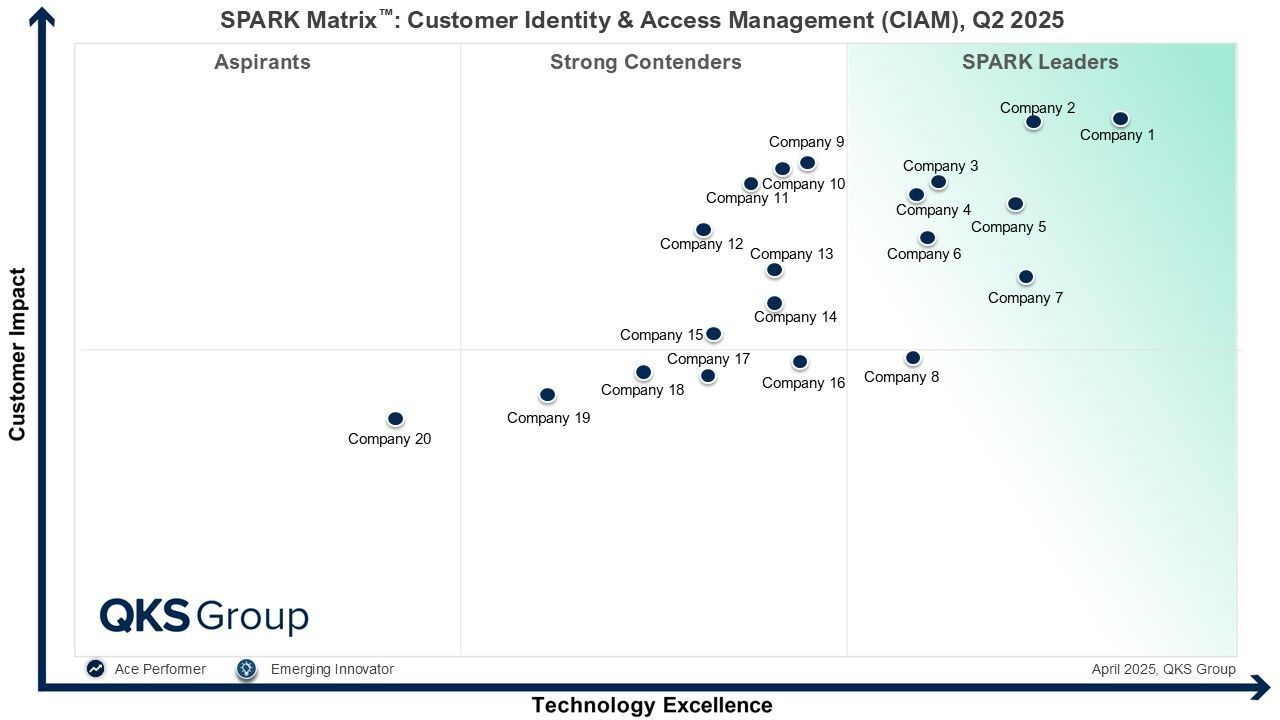
Why CIAM (Customer Identity and Access Management) Is Now a Big Tech Priority in 2026
In today’s digital world, businesses must make sure their customers can securely access online services while having a smooth, easy experience. This is where Customer Identity and Access Management (...
-

Technology Excellence and Customer Impact in Digital Threat Intelligence Management
In the rapidly evolving world of cybersecurity, digital threat intelligence management is becoming vital for organisations to protect themselves from sophisticated cyber attacks. The 2025 SPARK Matri...
-

SPARK Matrix™ In App Protection: A Complete Guide to In App Security Solutions
In 2025, application security remains one of the most important challenges for businesses and developers worldwide. The rapid growth of mobile, web, and desktop applications brings new opportunities-...
-

Governance, Risk & Compliance Platforms: Technology Benchmarking and Competitive Analysis
In today’s fast-changing business world, organizations face many risks — from regulatory changes and cybersecurity threats to operational failures and third-party vulnerabilities. To stay ahead, ente...
-

Bot Management Market: Technology Excellence and Customer Impact Analysis
In today’s digital world, automated bot attacks are one of the biggest threats to online businesses. Bots can scrape data, perform credential stuffing attacks, overload servers, and disrupt user expe...
-
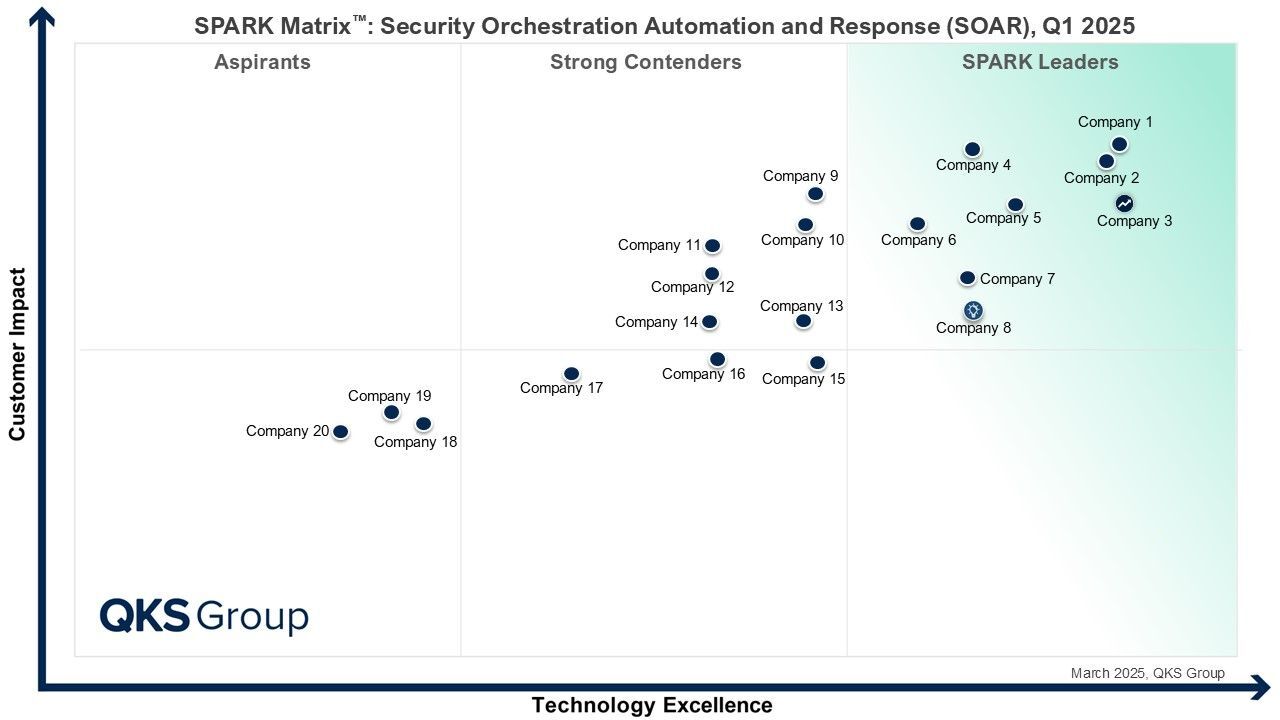
Strengthen Cyber Resilience with the Right Security Orchestration, Automation, and Response Platform
In today’s cybersecurity landscape, organisations are under constant pressure from advanced threats and rapidly evolving attack techniques. Security teams must act faster and more accurately than eve...
-

Strengthening Cyber Resilience with Advanced DDoS Mitigation Solutions
In today’s connected world, Distributed Denial of Service (DDoS) attacks continue to be one of the most damaging cyber threats. These attacks flood online systems with enormous volumes of traffic to ...
-

Identity Threat Detection and Response Platforms: Market Dynamics and Innovation Trends
The global Identity Threat Detection and Response (ITDR) market is rapidly emerging as a cornerstone of modern cybersecurity strategies. As organizations accelerate digital transformation and adopt h...
